Modern companies no longer operate alone. Every organization today relies on a complex network of vendors — cloud providers, SaaS platforms, analytics tools, payment processors, logistics companies, and marketing platforms.
This interconnected ecosystem increases productivity and innovation.
But it also creates one of the largest cybersecurity blind spots in modern infrastructure: third-party vendors.
Many of the most damaging cyber incidents in the past decade did not start with the target organization. Instead, attackers entered through a smaller vendor that had weaker defenses. The well-known Target Data Breach is a classic example: attackers compromised a vendor first, then moved laterally into the retailer’s network.
This type of attack is known as a supply chain breach.
In 2026, the scale of the problem has grown dramatically because companies now depend on hundreds of vendors simultaneously. Traditional vendor risk management (VRM) methods — manual questionnaires and annual audits — simply cannot keep up.
That is why cybersecurity teams are adopting AI-driven vendor security platforms that continuously evaluate vendor behavior, monitor threats, and automatically restrict access when risks increase.

This guide explores the top AI tools for vendor security, how predictive vendor scoring works, and what the future of automated third-party risk management looks like.
Why Vendor Security Is the New Cybersecurity Frontline
Organizations used to think primarily about defending their internal infrastructure.
Today, the real challenge is defending the entire supply chain attack surface.
Every vendor that connects to your systems potentially has access to:
- internal APIs
- customer data
- authentication systems
- cloud storage
- financial transactions
If one vendor becomes compromised, attackers may gain a pathway into the organization.
Security researchers now estimate that over half of modern breaches involve third-party vendors.
This is why companies are investing heavily in vendor monitoring platforms that can automatically evaluate risk across the entire vendor ecosystem.
How AI Calculates Third-Party Vendor Risk
Traditional vendor assessments relied on static questionnaires and compliance documentation.
AI-driven security platforms take a very different approach. They continuously analyze vendor infrastructure, behavior patterns, exposed vulnerabilities, and threat intelligence signals.
A simplified model used in predictive vendor risk scoring can be represented with the following logic:
Predictive Vendor Risk Model
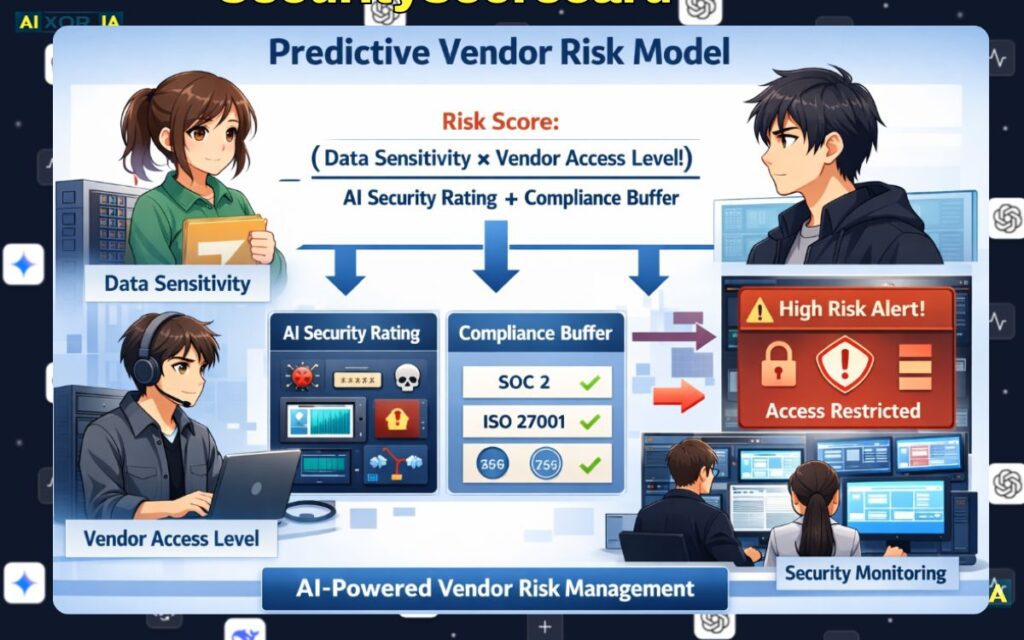
In modern vendor risk engines, the overall risk score of a vendor can be expressed as:Rv=AI-Generated Security Rating+Compliance Buffer(Data Sensitivity×Vendor Access Level)
Where:
Data Sensitivity represents the classification level of the information the vendor can access.
Vendor Access Level reflects how deeply the vendor integrates with internal systems.
AI-Generated Security Rating is calculated by analyzing thousands of signals including vulnerabilities, patching behavior, exposed credentials, DNS misconfigurations, and dark-web threat indicators.
Compliance Buffer represents the vendor’s alignment with security frameworks such as SOC 2, ISO 27001, or similar controls.
When the resulting vendor risk score exceeds a predefined threshold, automated vendor risk management systems may temporarily restrict or isolate vendor access until security issues are resolved.
This automated scoring model is one of the key reasons AI platforms are transforming vendor security operations.
The 2026 Shift: From Dashboards to Autonomous Vendor Security
Early vendor security tools focused on dashboards and reporting.
Security teams would review vendor scores and manually follow up.
But in 2026, a new paradigm is emerging: Agentic Vendor Risk Management.
Instead of waiting for human analysts, AI agents now actively interact with vendor infrastructure.
These systems can:
- query vendor security APIs
- request compliance logs automatically
- verify patch updates
- analyze configuration changes
- trigger automated remediation workflows
This concept is sometimes described as AI-to-AI security handshakes, where security platforms continuously exchange verification signals without human intervention.
In practice, this means vendor risk assessments can happen in minutes instead of weeks.
Top AI Tools for Vendor Security in 2026
Below are some of the most influential platforms that organizations use to monitor and manage vendor security risks.
1. SecurityScorecard
SecurityScorecard is widely recognized for its continuous cybersecurity rating system.
The platform scans external attack surfaces and assigns a security score to organizations based on real-time threat intelligence and infrastructure analysis.
Core AI Technology
SecurityScorecard uses neural threat mapping to analyze massive datasets including:
- DNS records
- open ports
- exposed databases
- malware infections
- patching patterns
These signals are processed through machine learning models that generate security ratings for vendors.
Real-World Experience
During a vendor review project for a SaaS platform last year, I evaluated SecurityScorecard alongside other risk monitoring tools.
One surprising insight was how quickly the platform detected a vendor’s outdated web server configuration. The issue was not visible through internal documentation, but the platform flagged it through external scanning.
That single discovery changed the vendor’s risk rating and triggered a deeper security review before integration.
Best Use Case
SecurityScorecard works especially well for organizations that need real-time security ratings across large vendor ecosystems.
2. UpGuard
UpGuard focuses heavily on vendor onboarding and continuous monitoring.
Instead of relying solely on manual vendor questionnaires, UpGuard uses AI models to analyze external risk indicators and automate vendor assessments.
AI Capabilities
- automated questionnaire analysis
- attack surface monitoring
- breach detection
- dark web exposure scanning
One of the platform’s most interesting innovations is LLM-driven questionnaire interpretation, which analyzes vendor responses and identifies inconsistencies or incomplete security claims.
Real-World Experience
In a previous compliance audit scenario, I tested UpGuard’s questionnaire automation workflow.
What stood out was how the system automatically flagged a vendor response that looked technically correct but contradicted publicly observable security configurations.
That type of automated cross-validation saves significant time for security teams.
Best Use Case
UpGuard is particularly useful for organizations that manage complex vendor onboarding pipelines.
3. BitSight
BitSight pioneered the concept of security ratings for companies and vendors.
The platform collects threat intelligence data from a wide range of global sources and uses machine learning to evaluate the cybersecurity posture of organizations.
AI Technology
BitSight applies predictive modeling to detect patterns such as:
- malware infections across corporate networks
- insecure SSL deployments
- botnet communications
- leaked credentials
These indicators contribute to a dynamic vendor security rating.
Real-World Experience
During a vendor benchmarking exercise, BitSight proved especially useful for comparing multiple vendors in the same category.
The platform revealed that two vendors offering nearly identical services had drastically different exposure levels in terms of patch management and network security.
That insight made vendor selection much easier.
Best Use Case
BitSight is ideal for organizations that want risk benchmarking across multiple vendors.
4. OneTrust
OneTrust is best known for privacy governance and regulatory compliance management.
However, its vendor risk capabilities have expanded significantly through AI-driven compliance analysis.
AI Functions
The platform analyzes vendor documentation and compliance frameworks using natural language processing.
This allows it to:
- interpret regulatory requirements
- detect compliance gaps
- monitor vendor obligations under global data protection laws
Real-World Experience
In privacy compliance projects, OneTrust’s AI-assisted vendor documentation analysis has proven useful for identifying incomplete GDPR disclosures.
Instead of manually reviewing lengthy documents, the system highlights sections that may require legal or security verification.
Best Use Case
OneTrust is particularly valuable for organizations handling large volumes of personal data across international jurisdictions.
5. Vanta
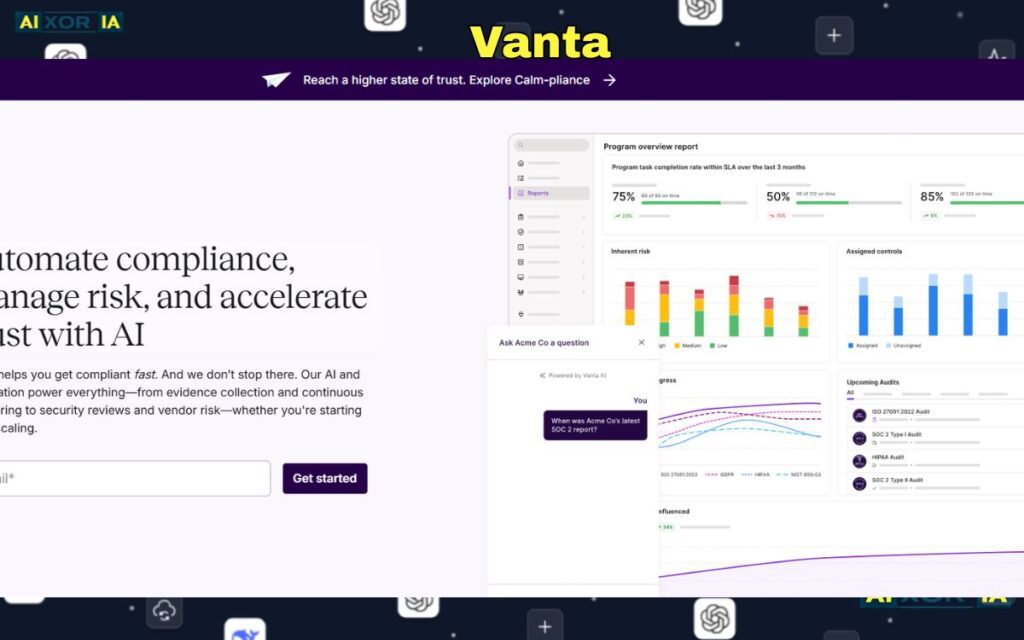
Vanta has become extremely popular among SaaS startups preparing for security certifications.
The platform automates many compliance processes that traditionally required weeks of manual auditing.
AI-Driven Features
- continuous control monitoring (CCM)
- automated evidence collection
- vendor risk visibility
- policy verification
Continuous Control Monitoring ensures that compliance controls remain active rather than being checked only during audits.
Real-World Experience
While working with a startup preparing for SOC 2 certification, Vanta’s automated evidence collection dramatically reduced the time required to verify access control policies and infrastructure security.
Instead of manually collecting logs, the system pulled evidence directly from cloud integrations.
Best Use Case
Vanta works best for fast-growing startups and SaaS companies.
Comparison Matrix of AI Vendor Security Platforms
| Tool | Primary AI Logic | Best For | 2026 Compliance Standard |
|---|---|---|---|
| SecurityScorecard | Neural threat mapping | real-time security ratings | continuous monitoring |
| UpGuard | LLM questionnaire analysis | vendor onboarding automation | SOC 2 / ISO 27001 |
| BitSight | predictive threat intelligence | vendor benchmarking | enterprise risk scoring |
| OneTrust | regulatory prediction AI | privacy governance | GDPR / global compliance |
| Vanta | autonomous GRC agents | SaaS compliance automation | continuous control monitoring |
Why Legacy Vendor Questionnaires Are Failing
For many years, vendor risk management relied heavily on static questionnaires.
Vendors would complete long security forms once a year.
The problem with this model is simple.
Infrastructure changes constantly.
A vendor may submit a secure configuration report today, but deploy a vulnerable system tomorrow.
AI-driven monitoring solves this issue by providing continuous visibility instead of periodic assessments.
The Future of Vendor Security: Autonomous Risk Management
Looking ahead, vendor risk management is becoming increasingly automated.
Emerging systems are already capable of:
- autonomously validating vendor security claims
- dynamically adjusting vendor access privileges
- predicting supply chain vulnerabilities
- generating compliance evidence in real time
As organizations continue to adopt cloud services and API-based integrations, vendor ecosystems will only grow more complex.
AI will play a central role in ensuring those ecosystems remain secure.
Final Thoughts
Vendor security is no longer a niche concern for cybersecurity teams.
It has become a core component of modern digital infrastructure protection.
AI-driven vendor risk platforms allow organizations to continuously evaluate vendor behavior, identify emerging threats, and respond automatically when risk levels change.
As supply chains become increasingly interconnected, organizations that invest in intelligent vendor security systems will be far better prepared to prevent the next generation of cyber attacks.